
A complete guide to juice jacking
Smartphones have become such a vital component of the modern lifestyle to the point that we are always glued to them. And as our time


Smartphones have become such a vital component of the modern lifestyle to the point that we are always glued to them. And as our time

It’s a busy week…you’re on the road and slammed with meetings. There won’t be much downtime between obligations, and you need to get creative about

Get Outdoors
In this issue:

We sure do miss heading out to a lake, throwing out a line and waiting for a fish to bite. But what really upsets us

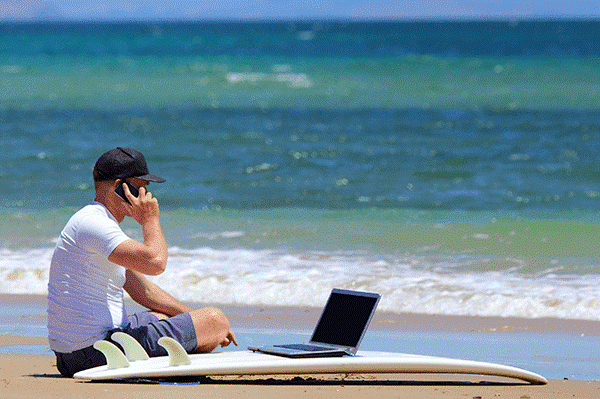
Surfing the web to any number of social media sites, articles, business sites, and content aggregators is pretty much a part of everybody’s daily routine.

Get Outdoors
In this issue:

Cyberattacks come in many different forms, with new methods being developed all the time. What’s bad is that personal information is now often stored online,

New Jersey is sometimes referred to as the Medicine Chest of the World since it is home to over 300 biotechnology companies and more than
Gone are the days when packing for your vacation meant simply grabbing some clothes from the closet and toiletries from the bathroom, tossing them in

A new owner of an established business often inherits great opportunity, but a host of unexpected problems can also come along. This happens even in
"*" indicates required fields
"*" indicates required fields