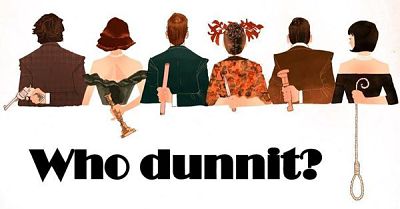
Clue is a murder mystery “whodunit” game that is popular the world over for quite some time. The object of the game is to determine who murdered the game’s victim, the infamous Mr. Boddy. Poor Mr. Boddy was murdered by one of the six suspects in the game. Who’s your favorite suspect? In the business world, no one wants their organization to be a victim of a crime, particularly a security breach. But, unfortunately, security breaches have become all too common.
When a security breach occurs, the game of “whodunit” begins.
Security breaches come both from within and outside of an organization; therefore, the list of suspects could be much longer than just six suspects as in the game Clue. As a result, tracking down the culprit can become very difficult.
In many of the breaches that you hear about in the news, it is often discovered that the actual breach occurred many months prior to it being identified. In one case, the breach occurred over two years prior to discovery. Imagine…having every communication in and out of your company monitored without your knowledge for two years! The investigators determined this by following the bread crumbs left behind—often these bread crumbs are in the security logs. IT Radix frequently finds small-to-medium businesses do not even have logging enabled nor retained for a sufficient length of time. In these cases, there may be limited to virtually no clues to identify the source of the breach. This can be disastrous because knowing what information was potentially exposed is difficult at best. As a result, we recommend tightening up access to information as much as possible, enabling auditing wherever reasonable, and ensuring that log files are backed up and retained for a period of time. We also recommend monitoring sources like the Dark Web for potential credential exposure. We recently discovered a client had over 50% of their employees’ email addresses and passwords available for purchase on the Dark Web.
In the interest of full disclosure, audit logs can become quite voluminous and often require special tools and skills to decipher their content. So, should something occur, it still requires detective work to determine what occurred. If you accept electronic payment of any form, you are obligated to enable and retain audit logs. Sadly, most organizations do not realize this requirement. In certain industries, you may be held to an even higher standard. Even if you have outsourced the actual payment processing, we find most organizations have more responsibility in this arena than they realize.
If a breach occurred in your organization, would you know how to respond?
Would you be able to deduce the culprit? Every organization should have, maintain and test a security Incident Response Plan (IRP). Similar to a disaster recovery plan, an IRP helps you determine your security risks, identify what security measures and corresponding auditing need to be put in place, and finally, guides the overall response should a breach occur. We find that at a minimum, a collaborative approach with your insurance agent/company, legal counsel, IT, and of course, management is usually needed to develop this plan. While we can implement technical solutions within your environment, an IRP is not the responsibility of IT alone. We can assist by implementing technical solutions such as the compliance features of Office 365, for example, but much more is required.
By planning, training and testing your team about security, you can help reduce the potential of a security breach and show the potential perpetrators that you really do have a “clue!” Need help? Give us a call.
First published in our January 2018 IT Radix Resource newsletter