500+ LinkedIn connections can open doors. It can lead to more business, new clients, and provide social proof to yourself or organization. However, getting to 500+ connections can seem like a daunting task, especially if you have a business to run. So how can you break through and become a LinkedIn power networker? Here are […]
How to get 500+ LinkedIn connections
Law Firm Relies on IT Radix to Ensure Key Data Are Secure

IT Radix has just added another top Morris County law firm to its growing list of clients. This new client aligned with IT Radix to ensure its technology architecture and key data were all up to date, maintained, backed up and secure. The lead attorney at this firm is quite accomplished and well known in civil trial law and has achieved a designation achieved by less than 2% of New Jersey based attorneys.
Customize your PDFs with Google Drive
Google Drive has become the go to cloud-based solution for many small businesses. There’s plenty of storage, it’s easy to organize, and collaborating as a team on one document is even simpler. However, when it comes to PDFs, people aren’t aware that it can do so much more.
April 2016 Connections Contest
How to optimize your VoIP performance
You’ve likely heard of VoIP: the innovative telephony solution that can dramatically cut costs and replace your traditional phone line. While it may sound appealing, you might have a few reservations. What if the call quality isn’t up to par? What if your staff is confused by the technology? What if you have to deal […]
IT Security Tip #12: DON’T use public WiFi until you read this
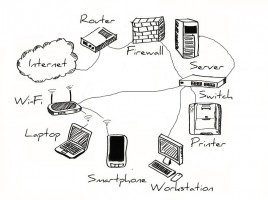
How is BYOD a security risk?
Bring your own device (BYOD) strategy is when an employee uses their personal mobile device to work with your company from anywhere. This strategy can bring about many advantages to your business such as increased efficiency and convenience. However, this can also bring a number of security risks for your IT infrastructure and data.
When Lunch‘n’Learn Becomes Eat’n’Meet
IT Radix has been inviting clients, prospects, guest and friends to our famous Lunch’n’Learn events for over 6 years now. We have covered a host of topics that are important to business owners and managers alike. Each year we plan out a series of subjects to cover ensuring that those who join us learn and get value for their time invested.
Business Identity Theft: Protect Your Computers and Networks

Business identity theft is serious business! Steve Cox, from the Better Business Bureau, stresses that “Business identity theft is a very real concern in today’s marketplace. From a criminal’s perspective, it is significantly more cost-effective to steal business identities than consumer identities.
IT Security Tip #11: You’ve been HACKED! What’s the first thing you should do?

Quick Tip: Call for help immediately.
Why: No matter how diligent you are about security, there’s always a chance you can get hacked. That’s why you need to put a plan in place NOW to protect yourself and your CLIENTS so damage is minimized. But what should you do if you find out you’ve been hacked?
First, contact your IT department (us) IMMEDIATELY. The faster we can address the attack—and determine the extent of the data, applications and machines compromised—the better your chances are of preventing much bigger problems.
- 1
- 2